Cybersecurity in Financial Services: Remaining compliant and reducing risk with automation
https://cybersecureforum.co.uk/wp-content/uploads/2021/06/LogRhythm-June-17th.jpg 960 640 Guest Post Guest Post https://secure.gravatar.com/avatar/cb2a67f15cd7d053d8e638a1df3fd67f?s=96&d=mm&r=gBy LogRhythm
Businesses in the financial services sector have to manage enormous risk, wealth and personally identifiable information (PII), all while meeting strict regulatory requirements.
As the proliferation of financial data continues to grow, organizations face the task of continuously protecting that information and keeping it secure, while maintaining a reputation in the financial sector. Despite this, many security teams lack the resources and funding to keep up with the evolving threat landscape and ecosystem of regulatory compliance rules.
The Complexity of Complying
For financial services organizations, cybersecurity is about minimising risk for both the customers and the business. This includes compliance, it is vital organizations reduce the possibility of further fines or other penalties by implementing security measures.
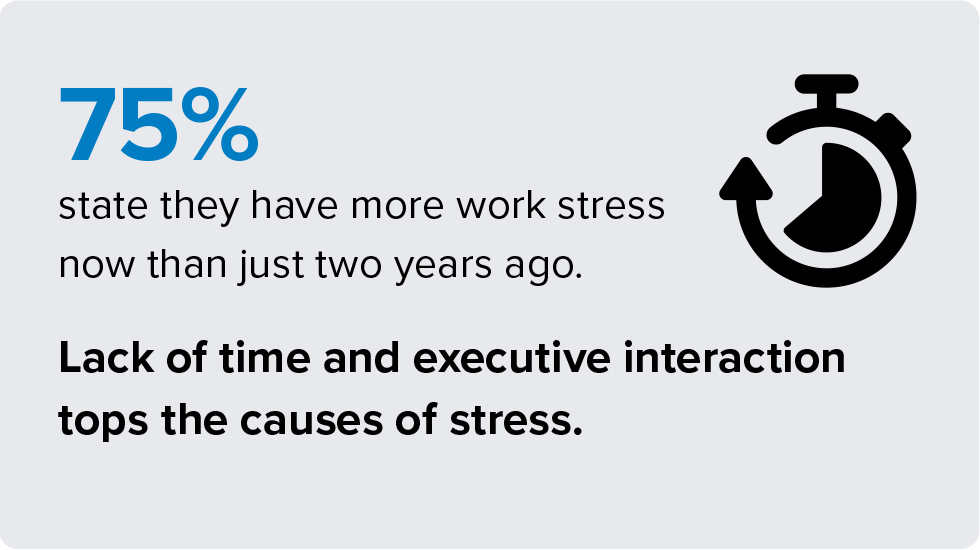
On top of this, security teams are often attempting to mitigate threats manually, increasing effort and stress. Analysts need to eliminate the time spent writing scripts, building rules and creating reports to allow focus on evolving attacks.
Automating Processes for Financial Security
Implementing prebuilt content which is specifically mapped to the individual controls of each regulation enables instant results that do the heavy lifting for you. Combining compliance automation software with Security Information and Event Management (SIEM) gives analysts the resources to comply with necessary mandates more efficiently and effectively than previous manual processes. A SIEM platform can facilitate security teams to improve detection, mitigation and response capabilities.
Furthermore, automation systems allow workflows to be more streamlined to help analysts combat evolving threats by removing manual tasks and enriching data with contextual details consistently.
An Expanding Compliance Environment
Looking forward, the financial sector is expected to face continued vulnerabilities in its technological offerings, both online and traditional brick and mortar. With compliance automation systems at the forefront, patterns of fraudulent activity will be detected at a greater rate, increasing the likelihood of mitigation before impact.
The compliance environment can only extend further, with more regulatory requirements coming into play. Financial organizations should be prepared for stricter security rules becoming a necessity to protecting both customer and business data.
LogRhythm’s offerings provide financial services organizations with industry-leading automation, compliance and auditing support, comprehensive reporting and protection against advanced cyberthreats – Learn more >